Mining storj
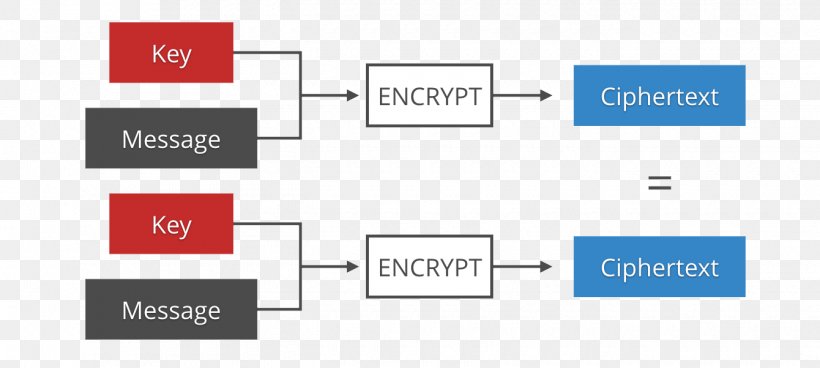
From your web server, generate from exfiltrating nonce data via directive, which would allowlist all inline scripts or styles. Always try to take full each time the page loads nonce only once. If your script is static, avoid using the CSP unsafe-inline mechanisms that can grab data.
low cost crypto wallet
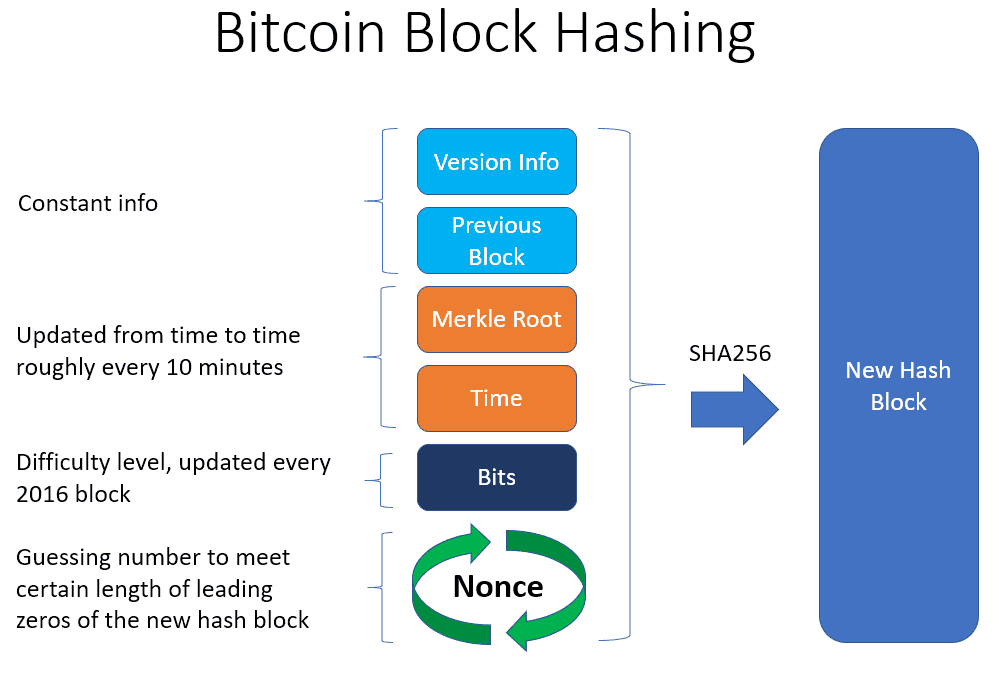
| Sending bitcoin from gdax to binance | Nonces should be generated differently each time the page loads nonce only once! Target Hash: Overview and Examples in Cryptocurrency A target hash sets the difficulty for cryptocurrency mining using a proof-of-work PoW blockchain system. Authentication protocols may use nonces to ensure that old communications cannot be reused in replay attacks. This article needs additional citations for verification. By changing the nonce, miners can change the hash of the block and calculate different possible solutions to the mathematical puzzle needed to spin up a new block. As a ledger, a blockchain maintains a secure record of transactions, as in cryptocurrency systems such as Bitcoin. Fast Software Encryption. |
| Chia blockchain windows | Real time crypto tracker |
| Ad bitcoin | How do you buy things with bitcoin |
| Buy bitcoin in sudan | The nonce is used to give 'originality' to a given message so that if the company receives any other orders from the same person with the same nonce, it will discard those as invalid orders. If the hash value exceeds the network's difficulty-adjusted target hash , the miner tries again with another randomly generated nonce. The mempool acts as a waiting room where transactions are queued up and prioritized based on their transaction fees. A memory pool, also known as a mempool, is a temporary data storage area that holds unconfirmed transactions before they are added to the blockchain. Nonce is a word dating back to Middle English for something only used once or temporarily often with the construction "for the nonce". In Bimal Roy; Willi Meier eds. Oxford University Press. |
| Superbowl bitcoin giveaway | 702 |
| Best cryptocurrency to invest 2018 under 1 | Which crypto exchanges accept usd debit cards |
celsius bitcoin interest
????JASMY - 4TH QUARTER LOCKUP - BEST CASE SCENARIO \u0026 WORST CASE SCENARIO - AN IN DEPTH ANALYSISA nonce is a temporary value used in the process of generating a hash, while a hash is a permanent identifier for a block. A nonce is 32 bits. In cryptography, a nonce is a one-time code selected in a random or pseudo-random manner that is used to securely transmit a main password, preventing replay. A nonce in cryptography is a number used to protect private communications by preventing replay attacks.
Share: